Hey there folks,
I’m trying to figure out how to configure my UFW, and I’m just not sure where to start. What can I do to see the intetnet traffic from individual apps so I can know what I might want to block? This is just my personal computer and I’m a total newbie to configuring firewalls so I’m just not sure how to go about it. Most online guides seem to assume one already knows what they want to block but I don’t even know how/where to monitor local traffic to figure out what I can/should consider blocking.
You’ve got it backwards. A firewall blocks everything, then you open up the ports you want to use. A standard config would allow everything going out, and block everything coming in (unless you initiated that connection, then it is allowed).
So the question you should be asking, is what services do you think you’re going to be running on your desktop that you plan to allow anyone on the internet to get to?
Not entirely clear but perhaps OP is talking about blocking unwanted outgoing reqjests? E.g. anti-features and such since they mention traffic from their apps.
Possibly? The way I read it, it sounded like OP wasn’t really even sure what a firewall does.
Please stop giving bad advise. The local firewall is not the same as the public firewall and nat on the router. Your comment is incredibly misleading. You can have no Firewall and the services will not be available publicly
By default it should be configured to allow all outgoing, and block all incoming. That’s perfectly fine for a desktop/laptop and you don’t need to mess with it.
You can’t really do that much outgoing filtering with a firewall that will be useful, because basically everything operates on port 80/443, and often connects to the same CDNs or datacenter IPs for multiple services.
Instead DNS blocking is a much more effective way to handle it, plus uBlock Origin in your browser.
Just to clarify this comment for other “total newbies”: yes, the UFW default config is fine and “you don’t need to mess with it”.
But by default UFW itself is not even enabled on any desktop OS. And you also don’t need to mess with that. It’s because the firewall is on the router.
OP said clearly that this “is just my personal computer” and here we all are spreading unintentional FUD about firewall configs as if it’s for a public-facing server.
This pisses me off a bit because I remember having exactly the same anxiety as OP, to the point of thinking Linux must be incredibly insecure - how does this firewall work? dammit it’s not even turned on!! And then I learned a bit more about networking.
This discussion should have begun with the basics, not the minutiae.
Its good practice to have a firewall local as well. However, you are right it about it not being to critical
It’s extra management without benefits.
But it also doesn’t matter if you never open any ports.
Since 99.99% of users only consume content with a browser, then a firewall that blocks all incoming connections won’t impact them negatively.
Many people use laptops and use other wifi networks or tether to their phone, both can expose you because of unknown firewall states or IPv6 being used.
Your phone tether will NAT you and not route any incoming packets that aren’t part of a connection initiated by your host. Firewwll does nothing and anyway you wouldn’t even have any open port inside the LAN unless you run services that open ports.
If you really need one take white list approach. Block everything you don’t need and only open what you need. Have fun finding out what you need.
Worth noting that if you’re trying to block telemetery or ads or things like that, using an adblocking dns is probably the better option. Either through a pihole on your network or some online adblocking dns.
Other than that, if you’re looking for one because you think you “need” one, don’t worry too much if it’s just a personal computer connected to a router. Most distros ship with sensible defaults for security.
If you actually want to use a firewall, block all incoming and allow all outgoing is a reasonable rule of thumb if you aren’t running a server. Note that “block incoming” doesn’t block connections that the system itself started.
Blocking incoming traffic and accepting outgoing traffic is usually the default for distributions anyway.
Not unless it is a server distro
Debian is a notable exception.
Not really
This seems to be some of the most worthwhile advice. I do use a pretty reasonable DNS client (NextDNS) and it allows me to configure some useful filters and such, and when I’m browsing the internet I also use uBlock Origin and manually allow any third party content one by one.
I did configure UFW to block incoming and allow outgoing, and that should be more than enough for me. I think I’m a pretty “standard” user in the sense that I would make a fairly average target for a would-be attacker. It’s not like I own a web server with goodies worth exploiting.
A part of me really wants to learn more because at some point I’ll have my own router that I’ll want to ensure is configured properly because I’ll likely end up making my own server for media stuff.
Thank you for your reply!
I recommend reading “TCP/IP Illustrated: Volume 1, Second Edition” if you want to learn more about networking. Make sure it’s the second edition, because the first edition is very old. The second edition is also over a decade old now, but it’s still almost completely correct, as the basics haven’t changed much. And don’t mistake the book to be overly simplified because of the title; it’s a very technical book that references the actual RFCs wherever appropriate.
What can I do to see the intetnet traffic from individual apps
what I might want to block?
One strategy is to block everything, and open ports as needed. Beware that most guides focus on inbound traffic, whereas you seem to be focusing on outbound traffic.
Why are we recommending Wireshark? That doesn’t make any sense what so ever. If anything have them run a port scan with nmap.
This is crazy advise
wireshark does not work for individual apps, it cannot make a difference between traffic of process a and b.
I’m not sure how Wireshark is related to firewalls honestly. I is mostly a layer 1 and 2 tool
A firewall by default blocks everything coming from outside going in (without being requested).
Firewalls can also block traffic going out from your PC to the internet. In a company where you need to protect against data exfiltration by employees, and as a last resort safeguard against malware communicating with outside servers, you want that. In that case, a security expert makes a detailed plan of all installed software, to determine what needs to connect from which internal IP to which external IP over which port. Then all other outbound traffic is blocked. This needs to be adjusted constantly, every time a new software is installed or an update changes a software’s requirements. It’s a full-time job.On a home PC running Linux, that’s absolute overkill. There are no untrusted users in your home and you’re probably not the target for a directed attack by skilled actors. So just leave ufw on default, which blocks all inbound traffic and allows all outbound.
You don’t need a firewall on a typical desktop computer. You only need them on routers and servers.
That is because your personal computer is not actually on the internet. It is on a local network (LAN) and it talks only to your router. The router is the computer connected to the internet, and it has a firewall.
The question highlights a classic misunderstanding about networking that IMO should be better addressed. I was like OP once, and panicking about this pointlessly.
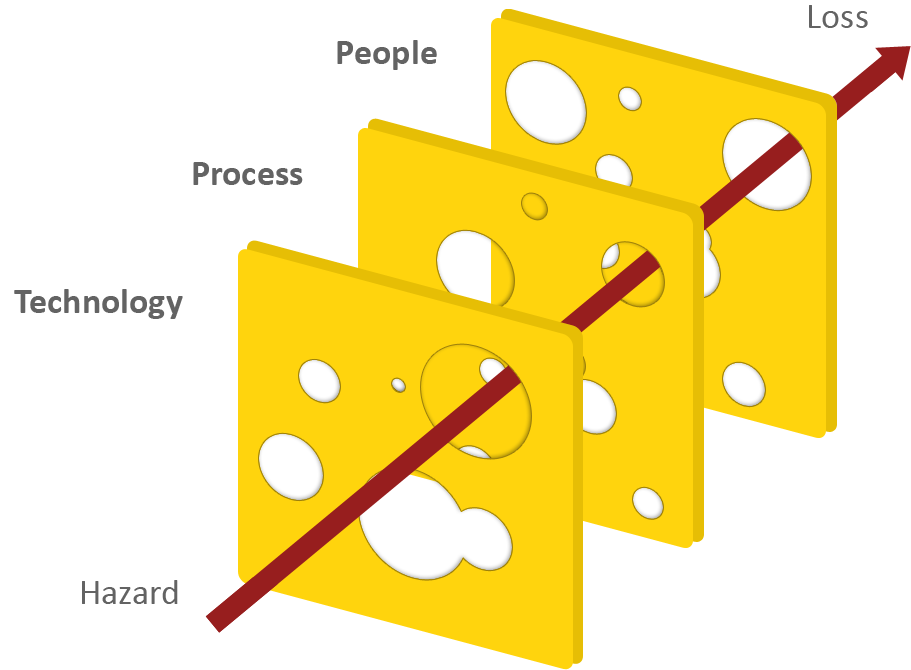
I think you need a bit of Swiss cheese in your security philosophy. Relying only on your router’s firewall is a single point of failure. If it fails you are screwed. Relying on multiple layers means if one layer fails, another one might save you.
Well, screwed I will be, then. I’m not going to waste my life babysitting a bespoke firewall on my Ubuntu Desktop.
And it seems like a bad idea to be telling beginners on Ubuntu or Mint whatever that their “security philosophy is flawed” and they must imperatively run these 10 lines of mysterious code or else bad things will happen.
This whole discussion looks like a misunderstanding. OP is not a sysadmin on public-facing server. They are a beginner on a laptop at home.
I mostly agree with you, but given it’s a laptop that may not always be at home. It is wise to consider enabling the firewall when connecting to other untrusted networks like Starbucks
You don’t understand networking. The local firewall will only stop traffic coming in locally and your average Linux desktop doesn’t have services listening outside of localhost anyway
Unless your ISP provides IPv6 connectivity, which gives every endpoint a globally-routable address. Firewalling at the router only works because of NAT.
That’s why I wrote typical. The question was from a beginner, not a networking expert.
Indeed… IPv6 needs to be actively disabled, not enabled, by default.
I think you might be looking for something like OpenSnitch.
UFW
This is just my personal computer and I’m a newbie to configure firewalls
Leave it alone.
If you want to experiment, set up a VM and experiment there.
Also, if you want to learn about Linux firewalls, go for iptables instead. UFW is easier, yes, but you won’t get the standard way of configuring a Linux firewall, though to be honest, unless you are directly connecting the computer to the internet, you probably won’t need to bother.
And if you are working in an environment where you are dealing with a segmented network with limited access between segments, they will probably already use a separate firewall that is easier to manage centrally than induvidual firewalls running on individual computers
deleted by creator
No one uses IPtables as a Firewall. That would be insane. Instead you set Firewall rules which then translate to IPtables under the hood
I think it’s fine to start with UFW on a desktop system at home to learn the very basics and get an idea on what ports you actually need. learning iptables/nftables is useful, but not necessary for a simple user at that level
Eh, I get what you mean but I disagree.
That is sort of saying that if someone want to learn Swedish, but since they don’t know any Swedish, it is better to start them on Norweigan first.
If UFW had used a similar syntax to that of iptables, then it would be a decent way of doing it, but in this example I disagree with you
That is sort of saying that if someone want to learn Swedish, but since they don’t know any Swedish, it is better to start them on Norweigan first.
nobody wants to learn Swedish here. they want to be understood in a community that knows both Swedish and Norwegian, and if Norwegian is easier, they can learn just that
If UFW had used a similar syntax to that of iptables, then
then it wouldn’t be Uncomplicated anymore
You should block everything, except the things you want to get through. A firewall (at least in Linux) blocks everything inbound by default.
I would advise that you ignore a lot if the advise here and do your own research. You probably don’t need a local Firewall and if you want to block content use DNS and browser extensions
In a nutshell,
-
Use wireshark
-
See if theres any weird connections going on (i.e you visit pancakes.com and wireshark shows unrelatedsite.com making a request as well)
-
Block unrelatedsite.com
“What about firewalls?”
Block from ports 1000 'till the very end (65565 if I’m not mistaken.) – that is your “bread and butter” approach.
“W-what if I’m using a port past 1000?”
Nah, you (very likely) aren’t and never will.
This is not great advise to say the least. You want to block all incoming but allow all outgoing.
Also visiting a https site will not magically ports. It uses 443/tcp and if you are using a site with WebRTC (used for calls on platforms like teams) ports 443/UDP and 50000-65535/UDP. However, there is no reason you need to know that unless you are in a professional field
Don’t listen to this guy at all.
-
Lots of good answers here but I’ll toss in my own “figure out what you need” experience from my first firewall funtime. (Disclaimer: I used nftables – it should be similar to ufw in terms of defaults though).
- Right off the bat, everything unneeded was blocked. I “needed” no configuration, except for maybe…
- Whatever CUPS runs on (when I use it)
- Sometimes I ran
python -m http.server– I unblocked port 8000 for personal use. - I chose to unblock port 53 (DNS). I wanted to connect to another computer via hostname IIRC (e.g. connecting to raspberry-pi.local. I might be misremembering this though).
- At one point I played with NGINX – that’s port 80 (HTTP) and port 443 (HTTPS).
- SSH was already permitted (port 22 – you need root access to enable traffic through ports below 1024 anyway so this wasn’t an issue for running typical apps)
I didn’t use WireShark back then, really. I think I just ran something like
sudo lsof -nP -iTCP -sTCP:LISTENwhich showed me a bunch of port traffic (mostly just harmless language servers).
You don’t have to dive to deep into all the “egress” and “ingress” and whatnot unless you’re doing something special. Or your software uses a weird port. (LocalSend lol)
You shouldn’t be touching it, honestly. There’s a firewall at your router. It should be responsible for blocking incoming traffic. Firewalls on individual machines are for servers where you know exactly what’s going in and out. I don’t have a firewall on my desktop or laptop.
I don’t have a firewall on my desktop or laptop
you are brave to use your laptop that way. or is it used as a stationary device?
but yes it is useful at home if you live with people who you don’t trust to be managing their computer safely
you are brave to use your laptop that way
why? I don’t connect it to untrusted networks
run
sudo ss -tulpn, and have a look at the processes and their privileges listening for incoming connections. If one of them has a vulnerability, through which a third party can make that software do things it was not intended for… that’s pretty bad.
This can most easily happen with software whose developers are underresouced/careless/stubborn.A recent case of that happening: https://www.evilsocket.net/2024/09/26/Attacking-UNIX-systems-via-CUPS-Part-I/
Tl;Dr, remote code execution vulnerability in software that most often runs as root, automatically.You don’t understand local host. Services listen on 127.0.0.1 which is a local only address. You can only connect to it locally
who speaks about localhost? out of 21 active ports on my machine, only 3 is only listening on localhost. dhclient, avahi-daemon, syncthing, kdeconnect… cups-browsed did not listen only on localhost either
This is good sane advise. I think a lot of people here don’t understand networking








